I’ve just gotten back from vacation and am a little behind on my weekly posts, so I wanted to share a short entry that builds on my previous:
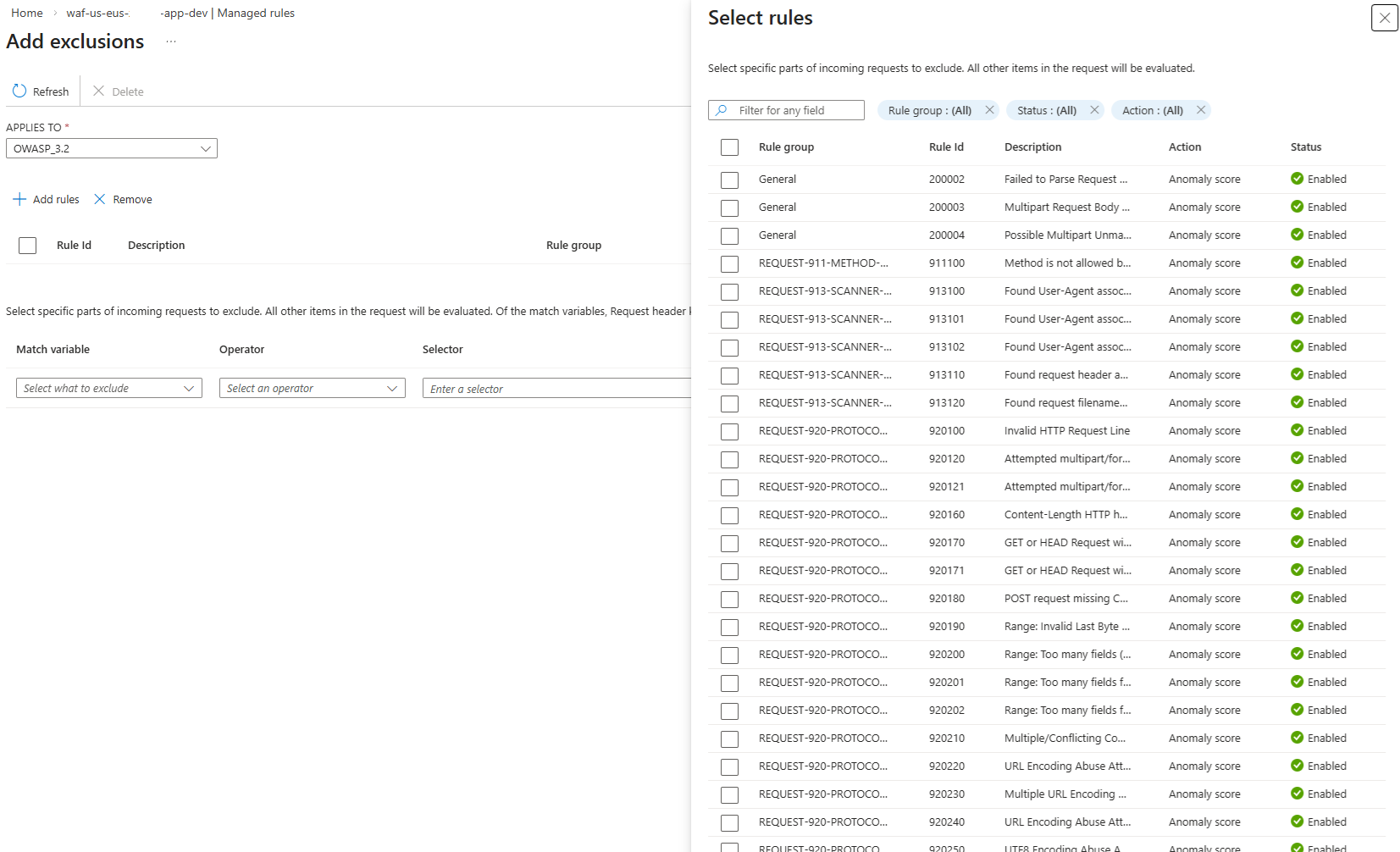
I typically manage WAF policies with Terraform so I can “Declaratively” configure and update the settings but there are times when I may not have access to the repository containing the Terraform code but need to quickly create exclusion rules in the WAF policy for troubleshooting. Those who have used the GUI to add an Exclusion to the Managed Rules of a Application Gateway WAF Policy may know that it’s a bit of a pain to select multiple Rule IDs as you can select multiple Rule IDs through scrolling the Select rules but as soon as you use the Filter for any field, attempting to select multiple Rule IDs that require different filter strings will only add the last one that was selected:
This is why during one of my recent projects where I had to configure multiple rules every day, I ended up importing the WAF policy into my Terraform code to perform the updates as I did not have access to the repository (I may write another post to demonstrate how I did this in the future).
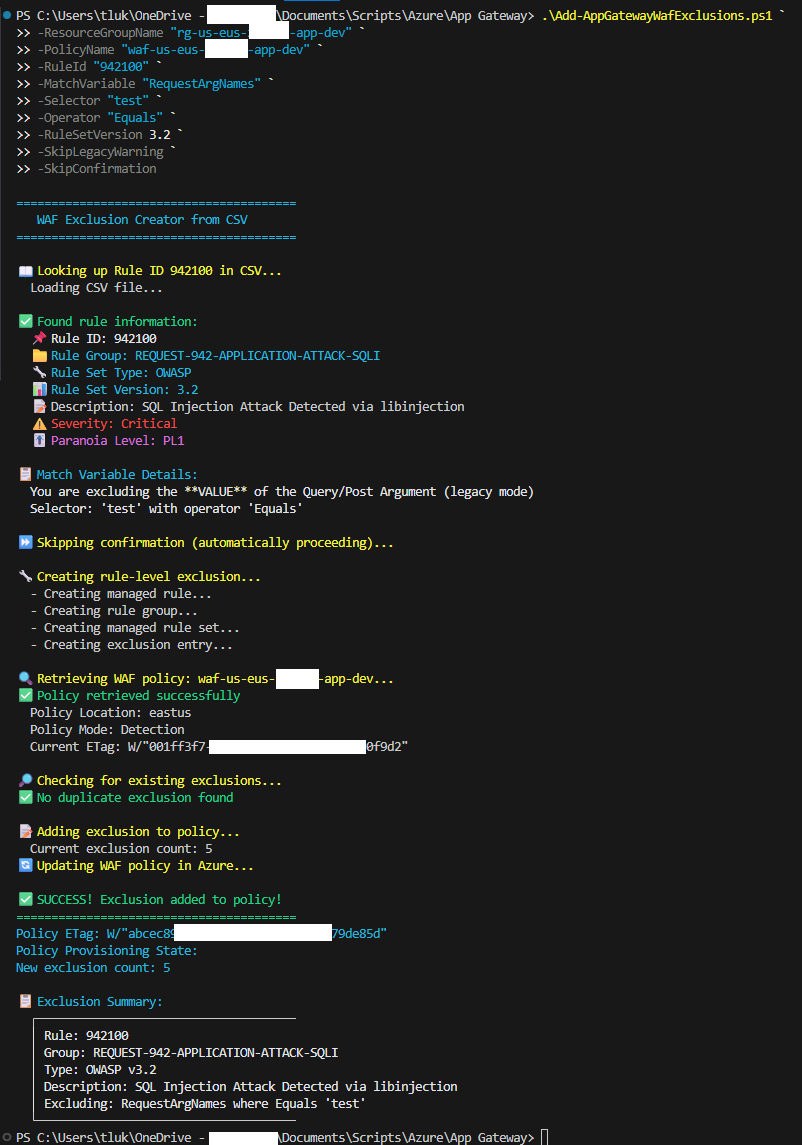
In scenarios where I do not have enough time to import and use Terraform to manage the rules, I use a script to add the rules so the process is less painful and slightly faster than using the GUI. The script can be found in my GitHub repository here: https://github.com/terenceluk/Azure/blob/main/App%20Gateway/Add-AppGatewayWafExclusions.ps1
This script uses a CSV with the Rule IDs as listed here in the Microsoft documentation: https://learn.microsoft.com/en-us/azure/web-application-firewall/ag/application-gateway-crs-rulegroups-rules?tabs=drs22%2Cowasp32 so that we can limit the amount of parameters that need to be passed (e.g. Rule Set Type, Rule Group Name and Rule Set Version).
My previous post demonstrates a way to export the list, although only for OWASP 3.2 (I’ll have to find time to update that script to handle DRS as well), but for this CSV file, I simply use Generative AI to create the file by pasting the web page content in. The CSV as update-to-date as today on February 18, 2026 can be found here: https://github.com/terenceluk/Azure/blob/main/App%20Gateway/RuleIDs-Feb-18-2026.csv
The execution will look as such:
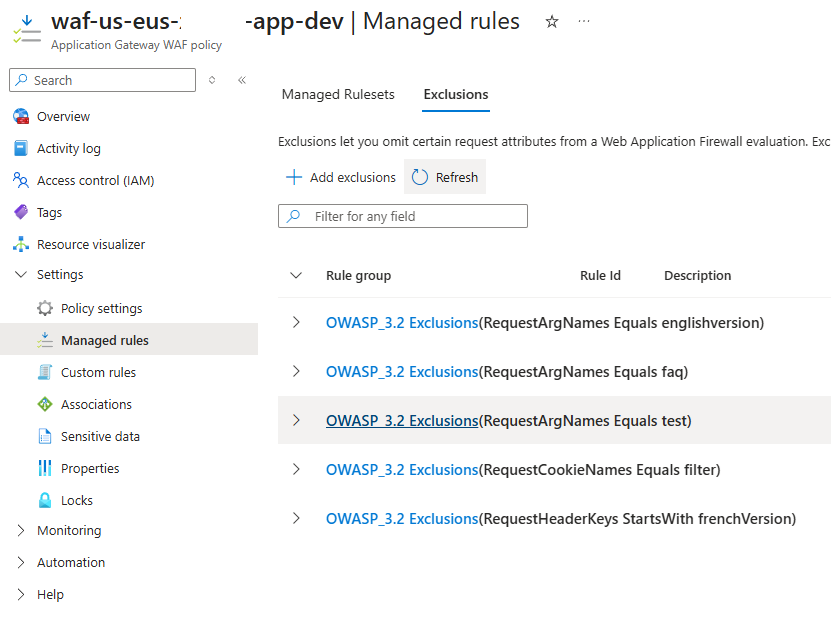
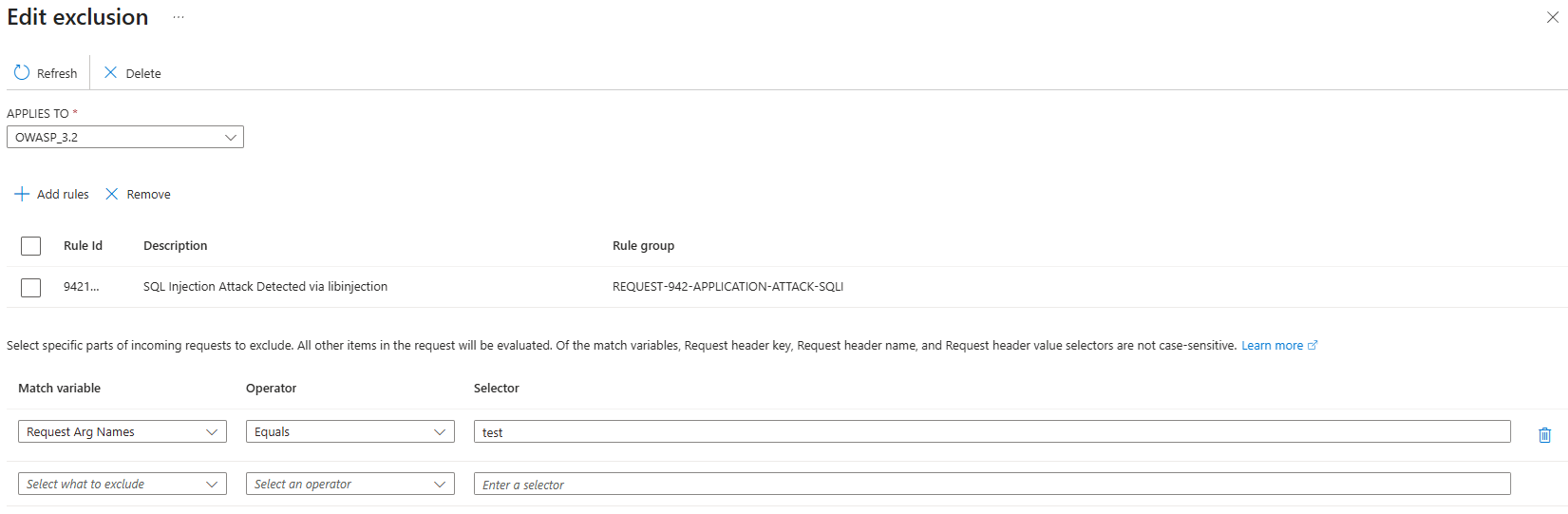
Once successfully executed, the rule will be configured for the WAF policy:
I hope this provides a quick way to add Managed Rules Exclusions to anyone who may have to do this in a whim.