As a continuation of the AD FS deployment from two of my previous posts:
Deploying a redundant Active Directory Federation Services (ADFS) Web Application Proxy servers on Windows Server 2019
https://blog.terenceluk.com/deploying-redundant-active-directory-21/
Deploying a redundant Active Directory Federation Services (ADFS) farm on Windows Server 2019
https://blog.terenceluk.com/deploying-redundant-active-directory/
This post serves to demonstrate the deployment of Duo to provide two-factor authentication for ADFS services using browser-based federated logins.
Deployment instructions as demonstrated in this post can be found directly from Duo here: https://duo.com/docs/adfs
Prerequisites
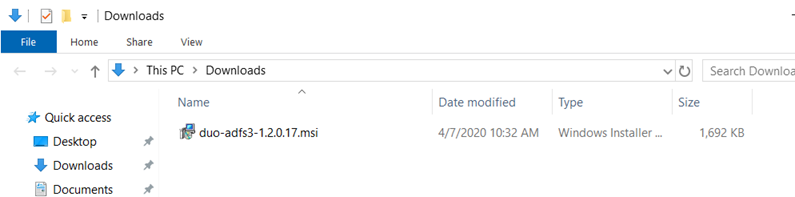
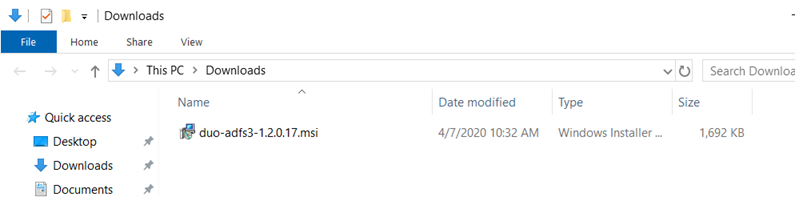
Download the DUO AD FS installer package for Windows 2012 R2 and later here: https://dl.duosecurity.com/duo-adfs3-latest.msi
Copy the file to your internal ADFS in your farm.
View the checksums for the Duo downloads here: https://duo.com/docs/checksums#duo-ad-fs
Retrieve Duo Configuration Parameters
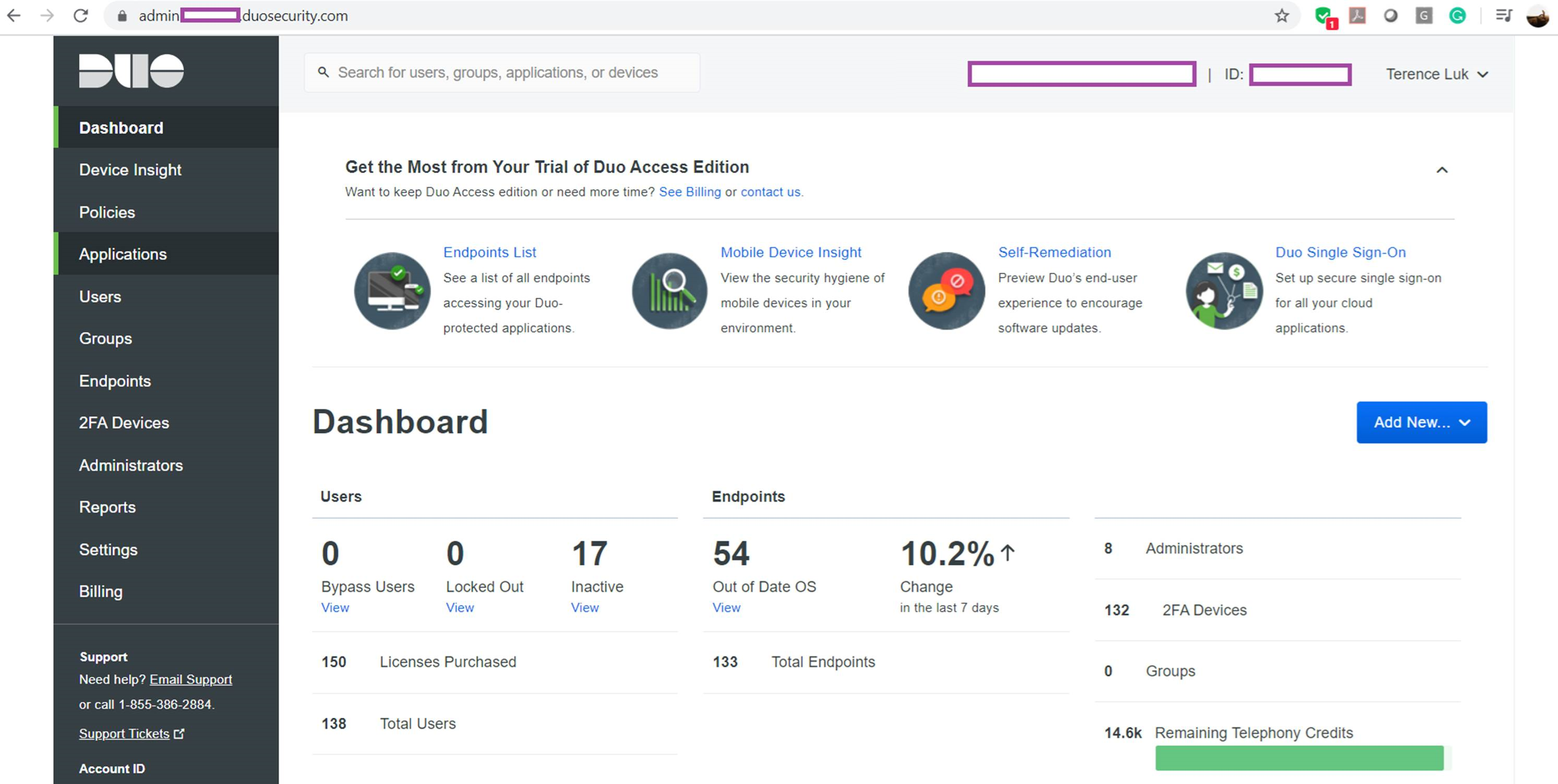
Begin by logging onto the Duo Admin Panel (https://admin.duosecurity.com/) with an administrator account:
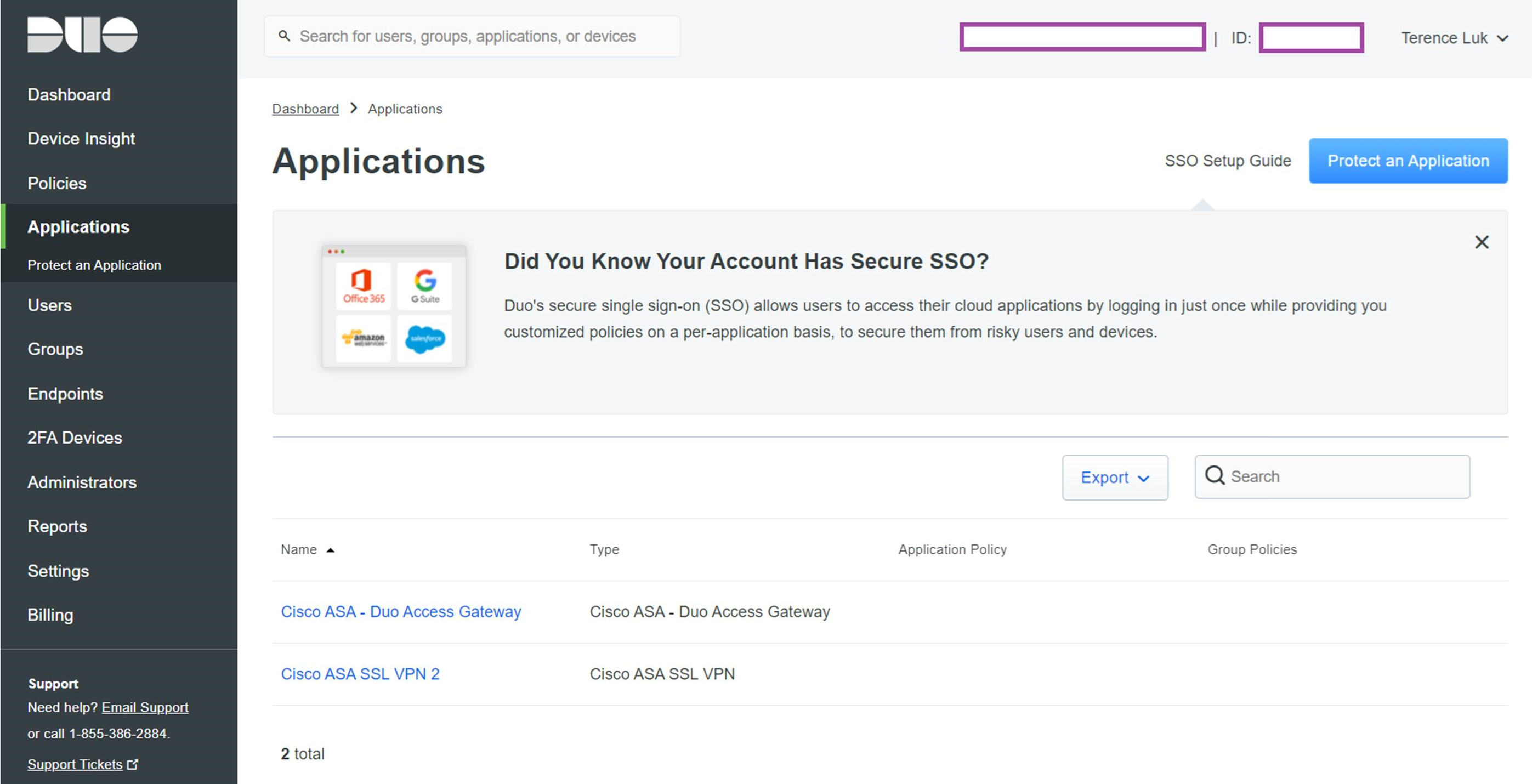
Navigate to Applications and click on Protect an Application
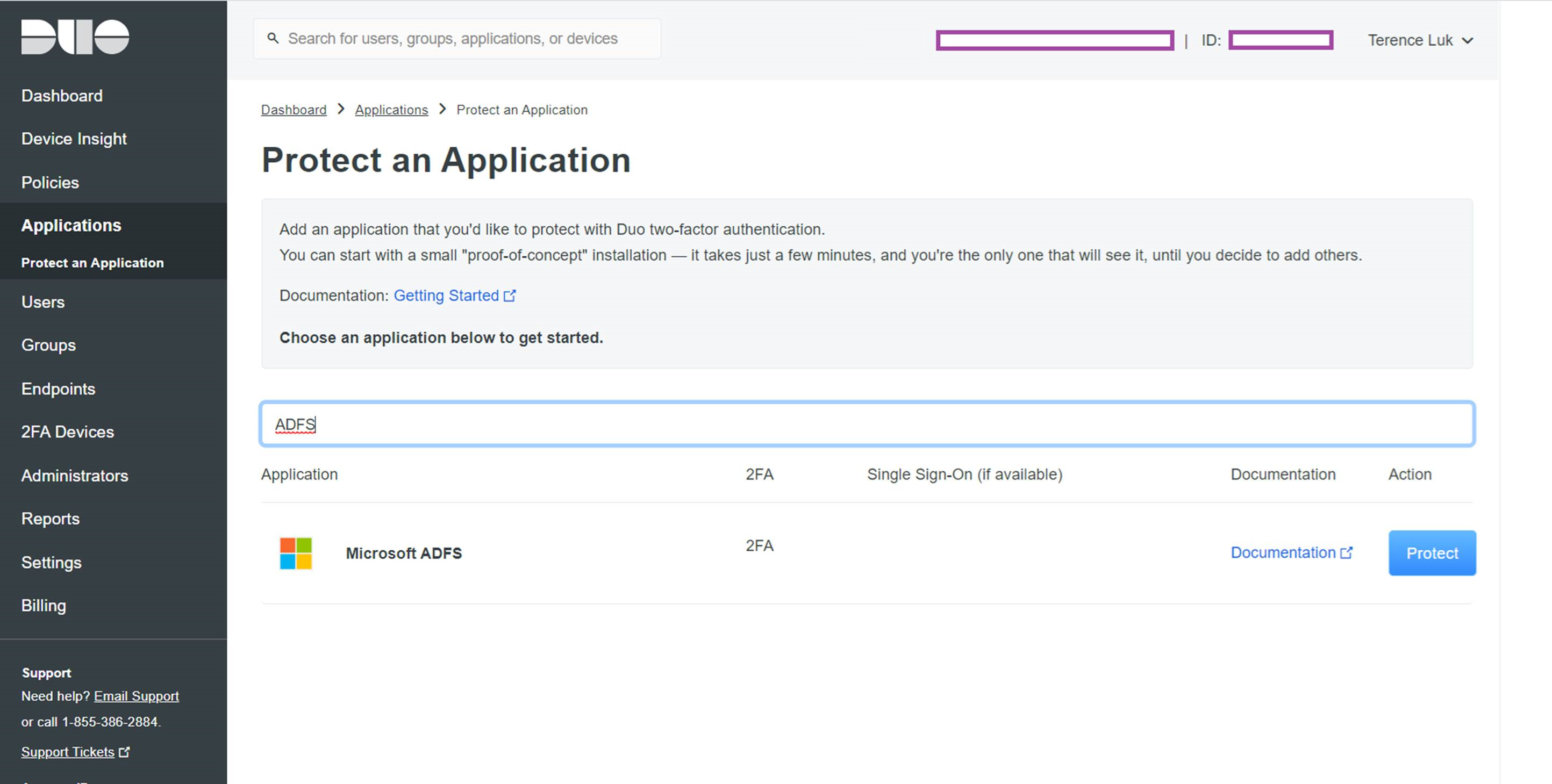
Type ADFS into the search field to locate Microsoft ADFS in the applications list then click on the Protect button to the right:
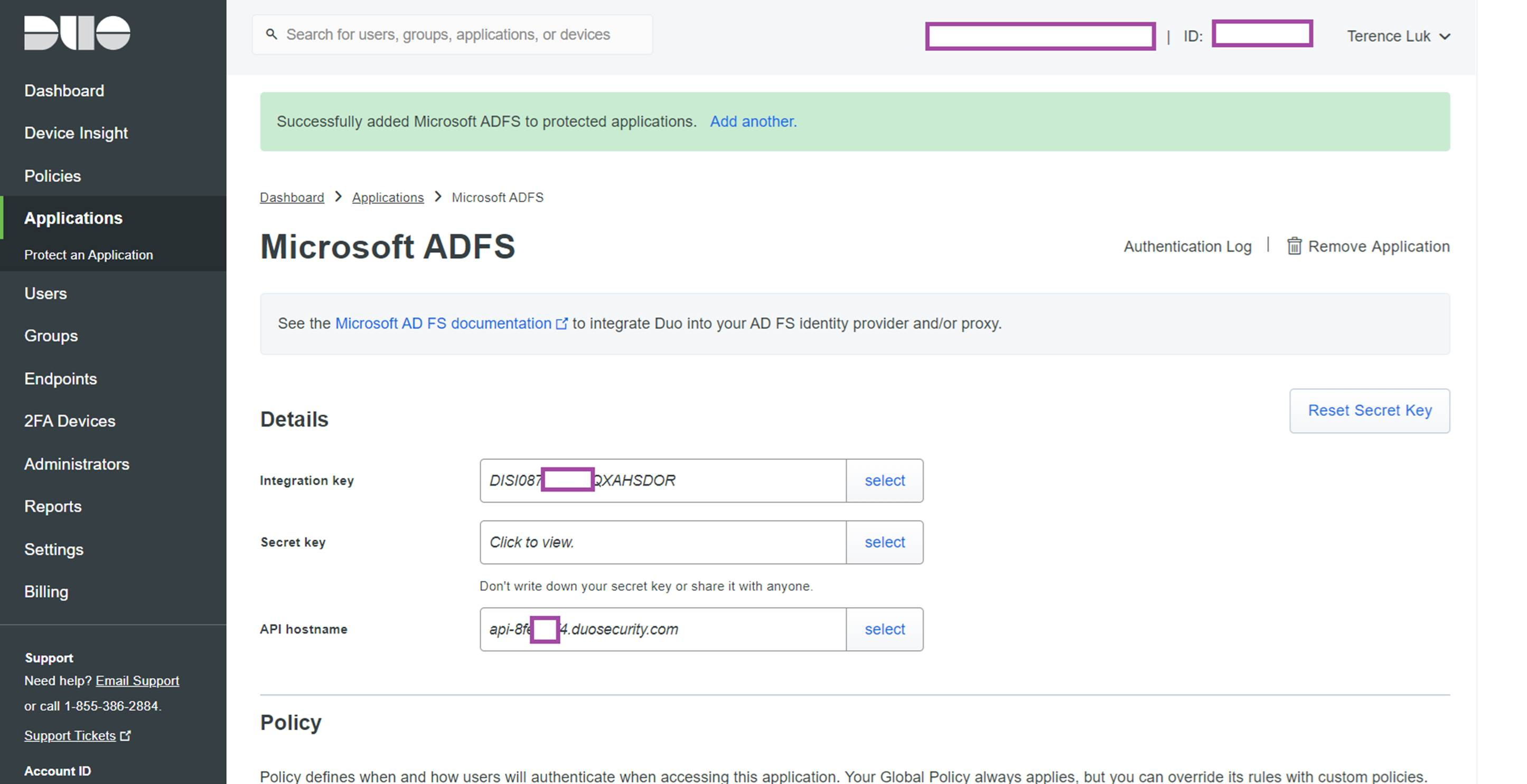
The following details will be displayed:
- Integration key
- Secret key
- API hostname
Copy the 3 text strings down into notepad as you will need them for the deployment later:
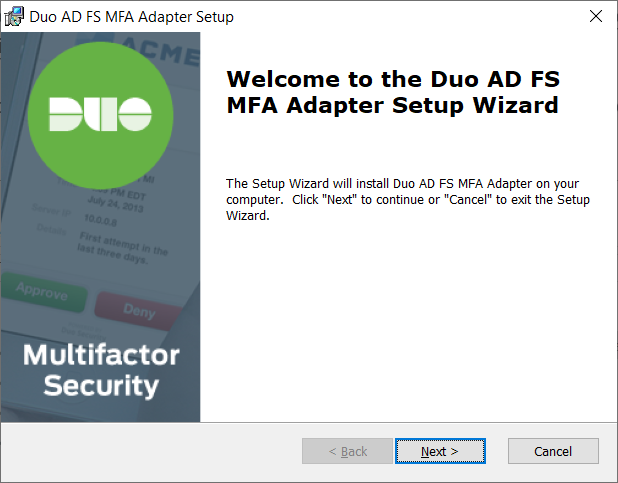
Install DUO MFA Adapter onto ADFS Servers
Log onto your internal ADFS server hosting the primary WIN database and run the duo-adfs3-1.2.0.17.msi MSI installer:
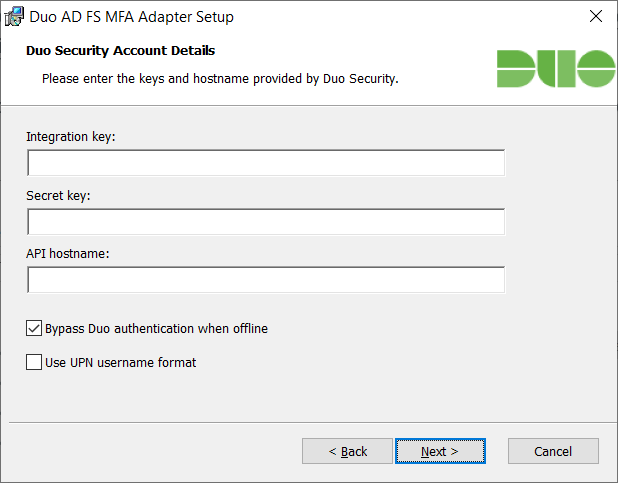
Enter the previously documented strings for:
- Integration key
- Secret key
- API hostname
Then decide whether you want to enable or disable the following 2 configuration parameters:
- Bypass Duo authentication when offline
- Use UPN username format
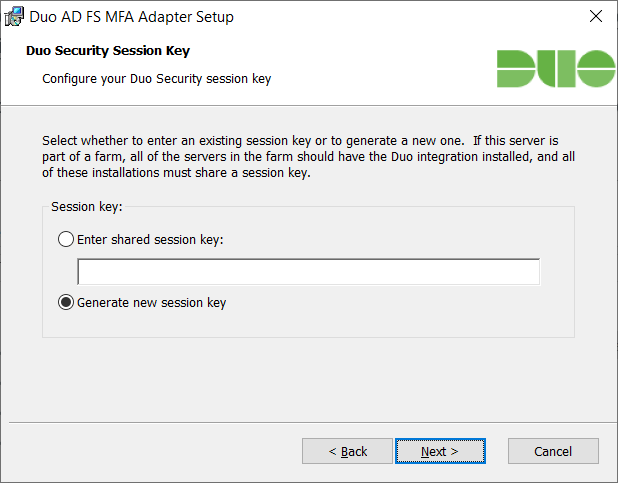
If you only have one ADFS server in your farm then select either of the option would not matter. However, if you have more than one ADFS server or plan to deploy an additional one in the near future then select Enter shared session key option and generate a unique key with the following PowerShell cmdlets:
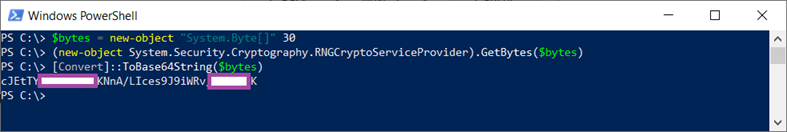
$bytes = new-object “System.Byte[]” 30
(new-object System.Security.Cryptography.RNGCryptoServiceProvider).GetBytes($bytes)
[Convert]::ToBase64String($bytes)
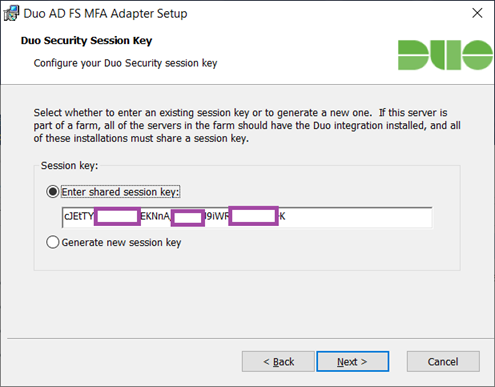
Place the unique key into notepad so you can use it for the deployment of the next ADFS server and then paste it into the Enter shared session key field:
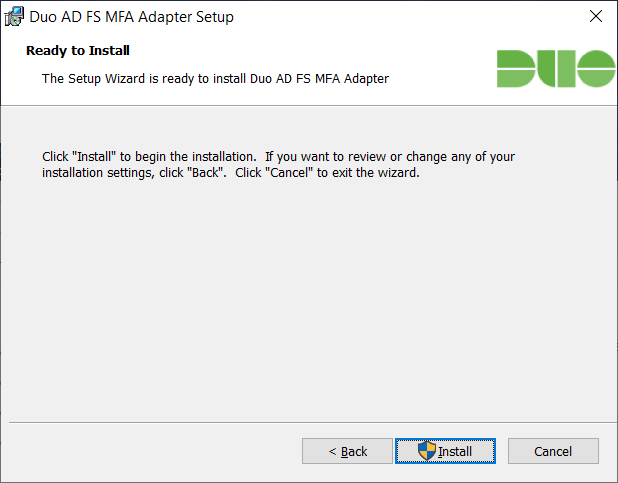
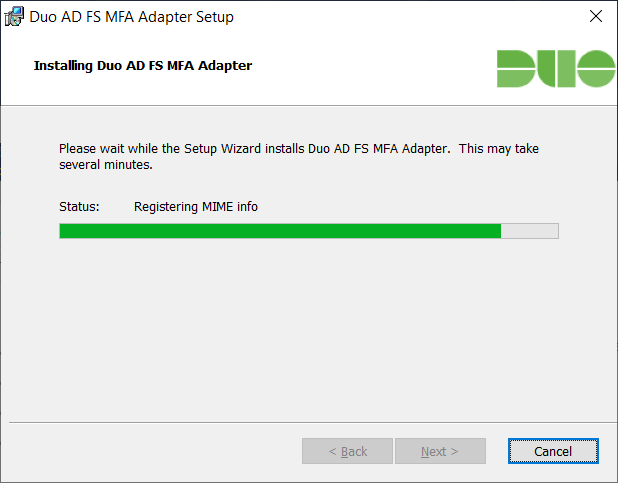
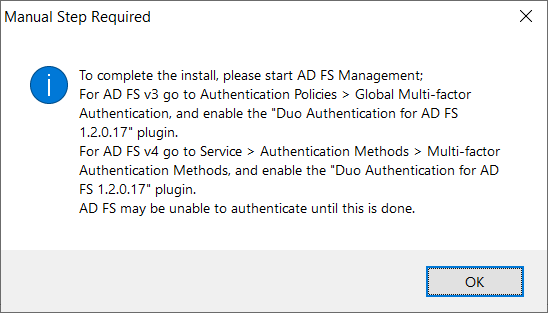
Proceed with the install:
The following prompt will be displayed upon completing the install:
Repeat the steps above for the additional ADFS servers in the farm.
Configuring AD FS to use DUO for MFA
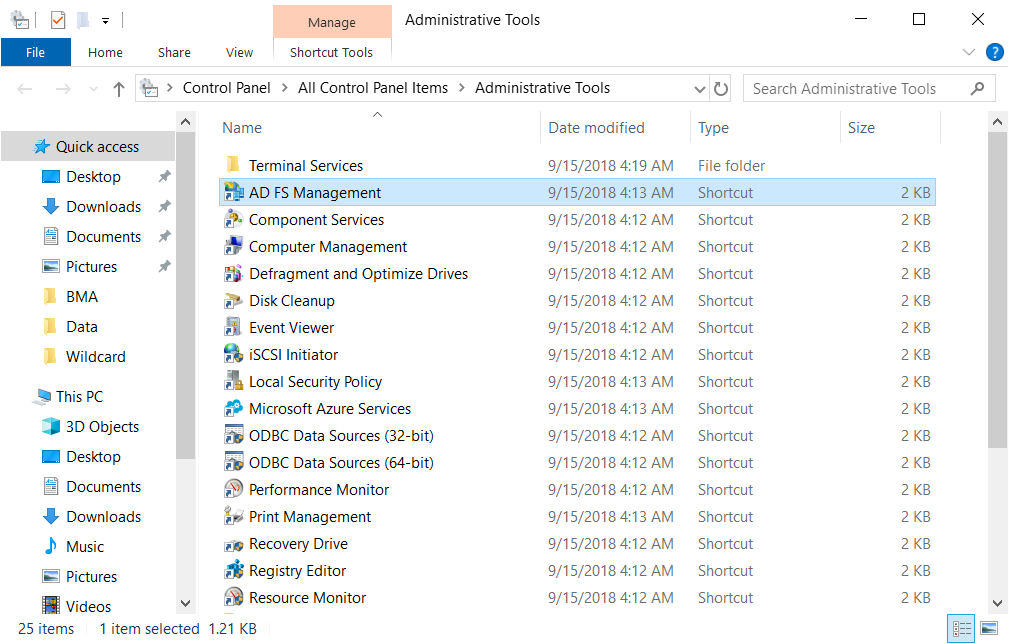
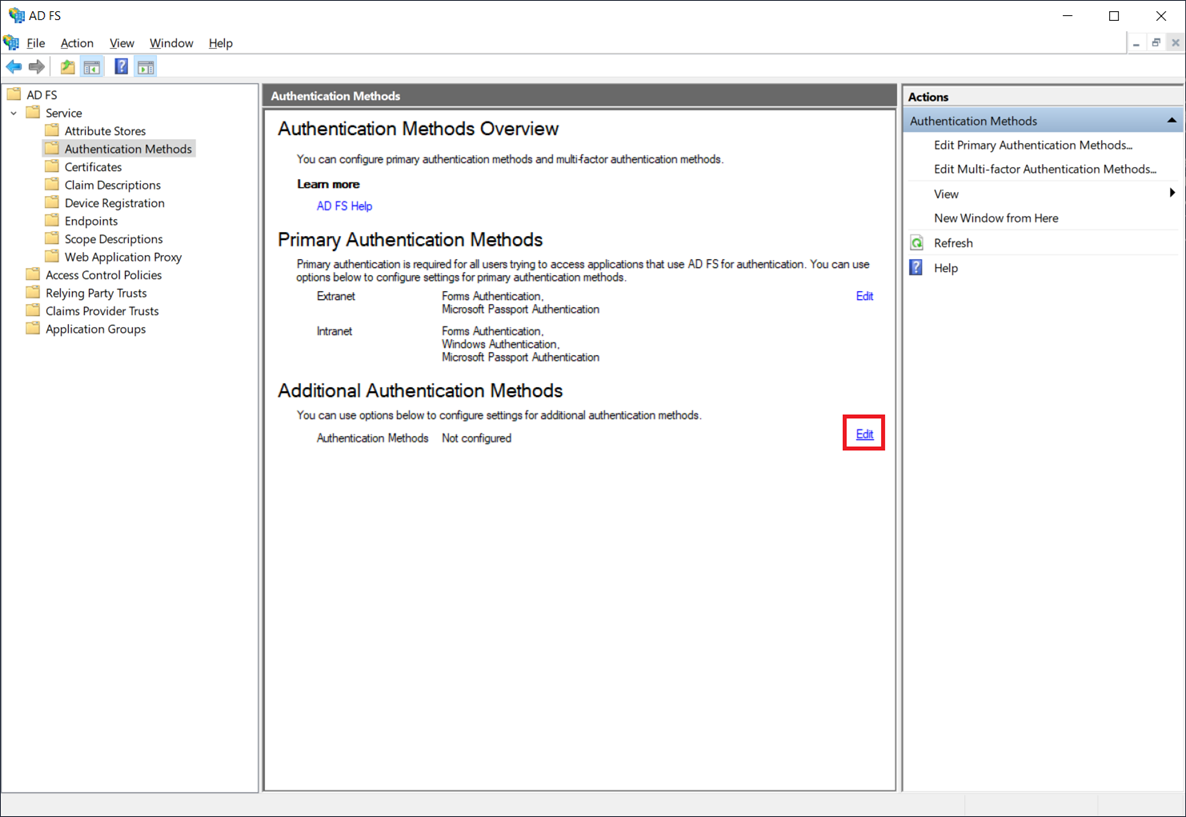
Launch the AD FS Management console:
Navigate to AD FS > Service > Authentication Methods and click on the Edit link for Additional Authentication Methods:
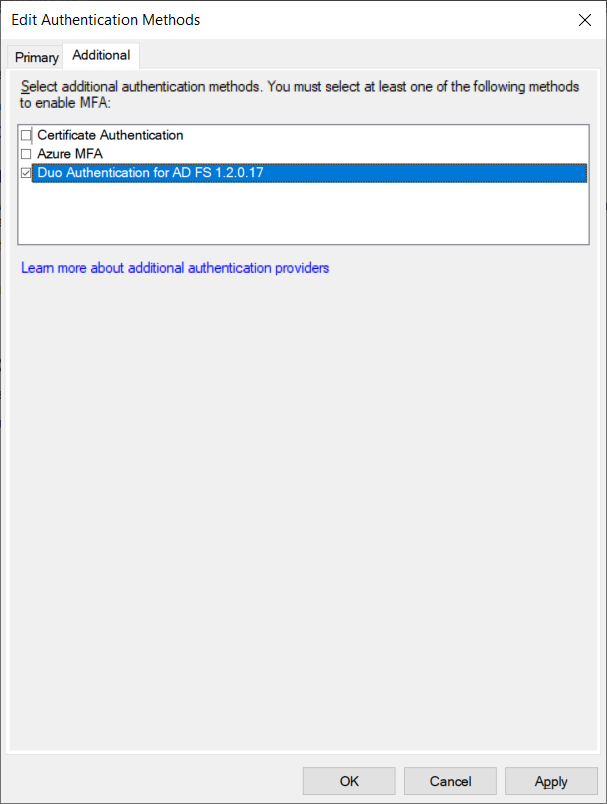
In the Edit Authentication Methods window, select Duo Authentication for AD FS 1.2.0.17 and click OK:
The ADFS farm is now ready to leverage the Duo Authentication for two-factor authentication.
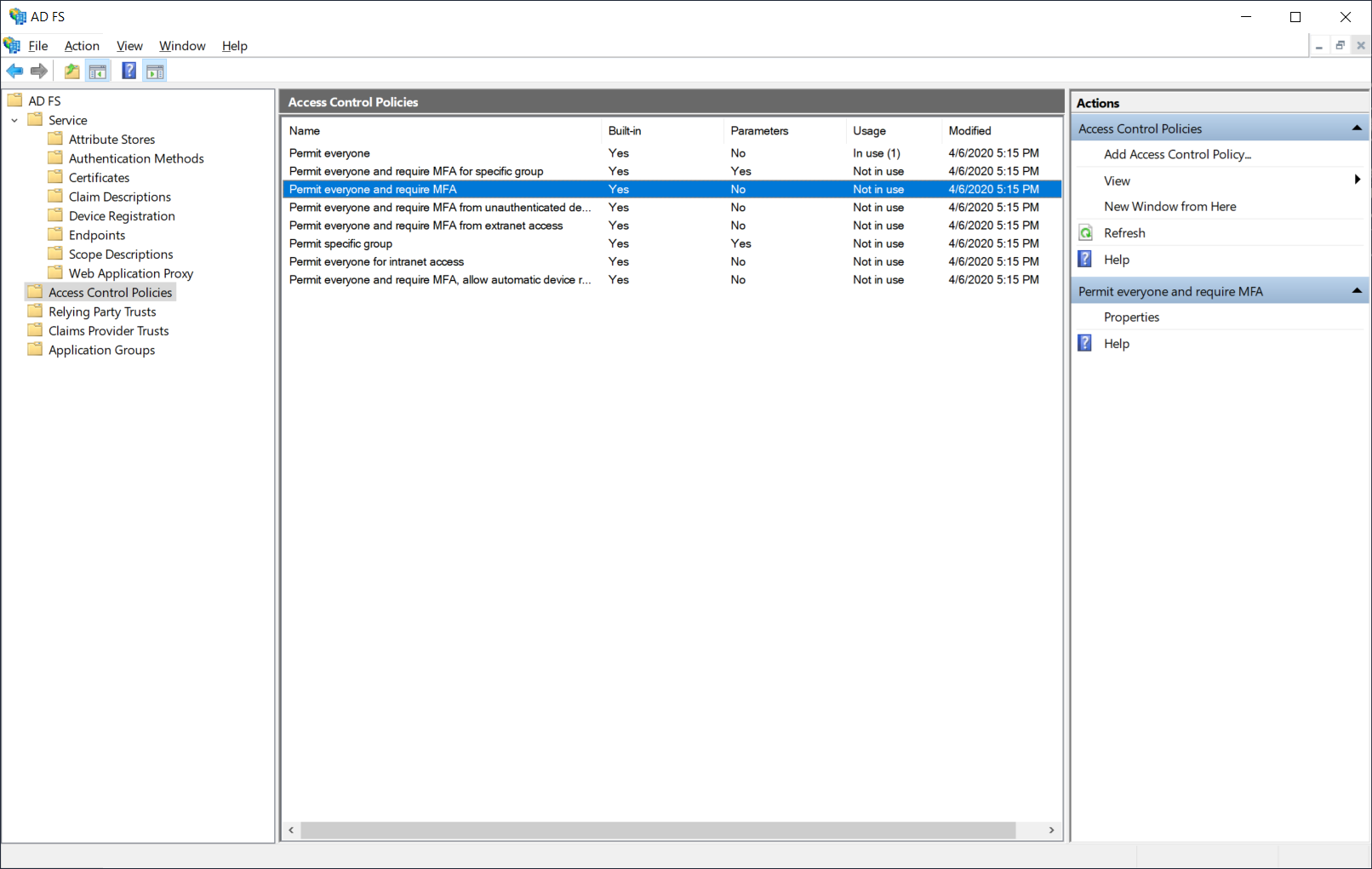
Depending on the requirements in your environment, the default Access Control Policies may be sufficient but if it isn’t, you can configure additional ones by navigating to ADFS > Access Control Policies:
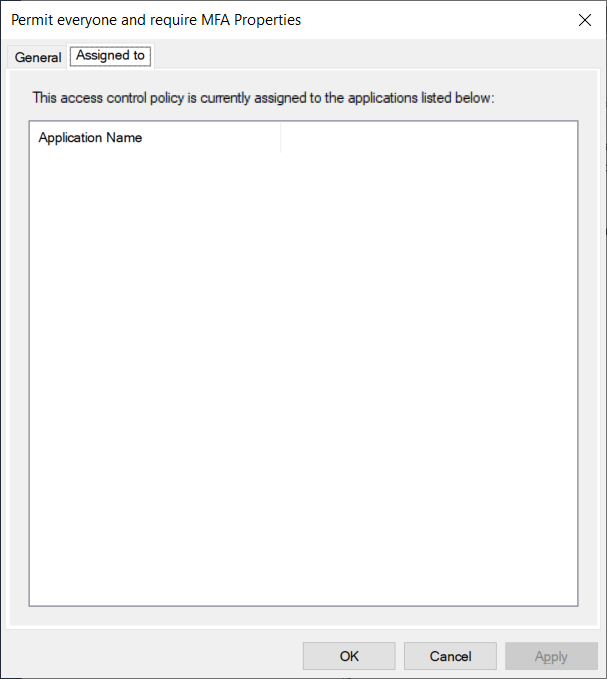
Note how the default Permit everyone and require MFA policy is not currently in use by any applications in this environment.
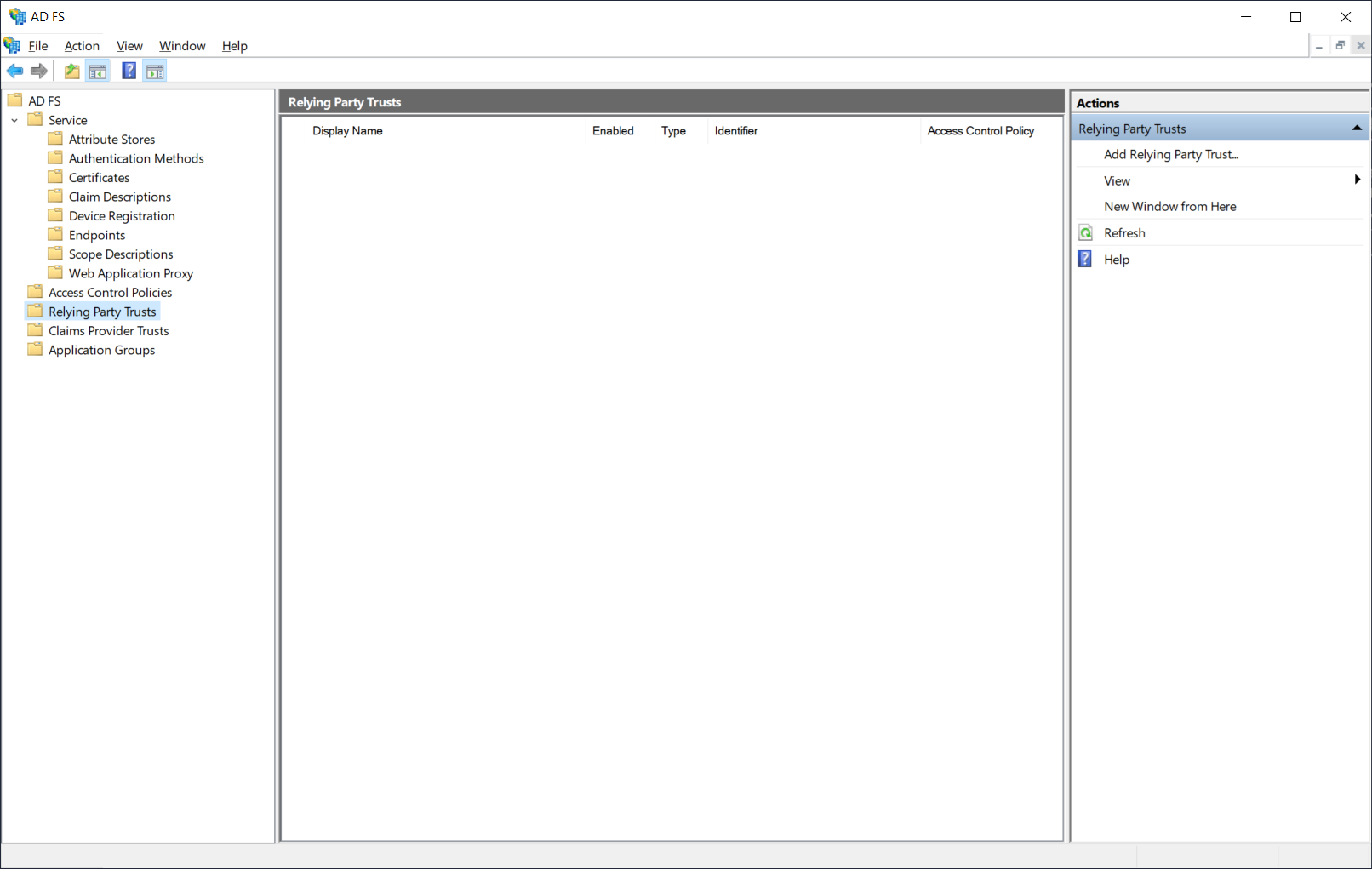
This environment also does not have any Relying Party Trusts (applications using AD FS for claims based authentication) configured:
Configuring Content Security Policy (CSP) on AD FS 2019
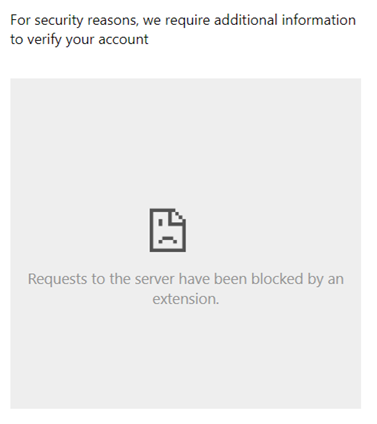
As of Windows Server 2019, the Content Security Policy security feature was introduced to secure ADFS and therefore the inline DUO prompt will not load properly without adding the Duo API hostname with the format api-xxxxxxxx.duosecurity.com into the Content Security Policy security configuration:
Option #1 – If Content Security Policy (CSP) has not yet been set on AD FS 2019, run the following command to set CSP allowing the Duo Prompt:
Set-AdfsResponseHeaders -SetHeaderName “Content-Security-Policy” -SetHeaderValue “default-src ‘self’ ‘unsafe-inline’ ‘unsafe-eval’; img-src ‘self’; frame-src api-xxxxxx.duosecurity.com ”
Option #2 – If you have set existing CSP in AD FS 2019, run this PowerShell script to append the necessary changes:
$apihostname = “api-XXXXX.duosecurity.com”
$CSP = ((Get-AdfsResponseHeaders | Select -ExpandProperty ResponseHeaders).’Content-Security-Policy’)
$CSP = $CSP + “; frame-src ” + $apihostname
Set-AdfsResponseHeaders -SetHeaderName “Content-Security-Policy” -SetHeaderValue $CSP
Please remember to replace api-xxxxxx.duosecurity.com in both of the options above with the Duo hostname you copied from the Duo administration portal earlier.
Testing Duo two-factor authentication on the idpinitiatedsignon.htm page
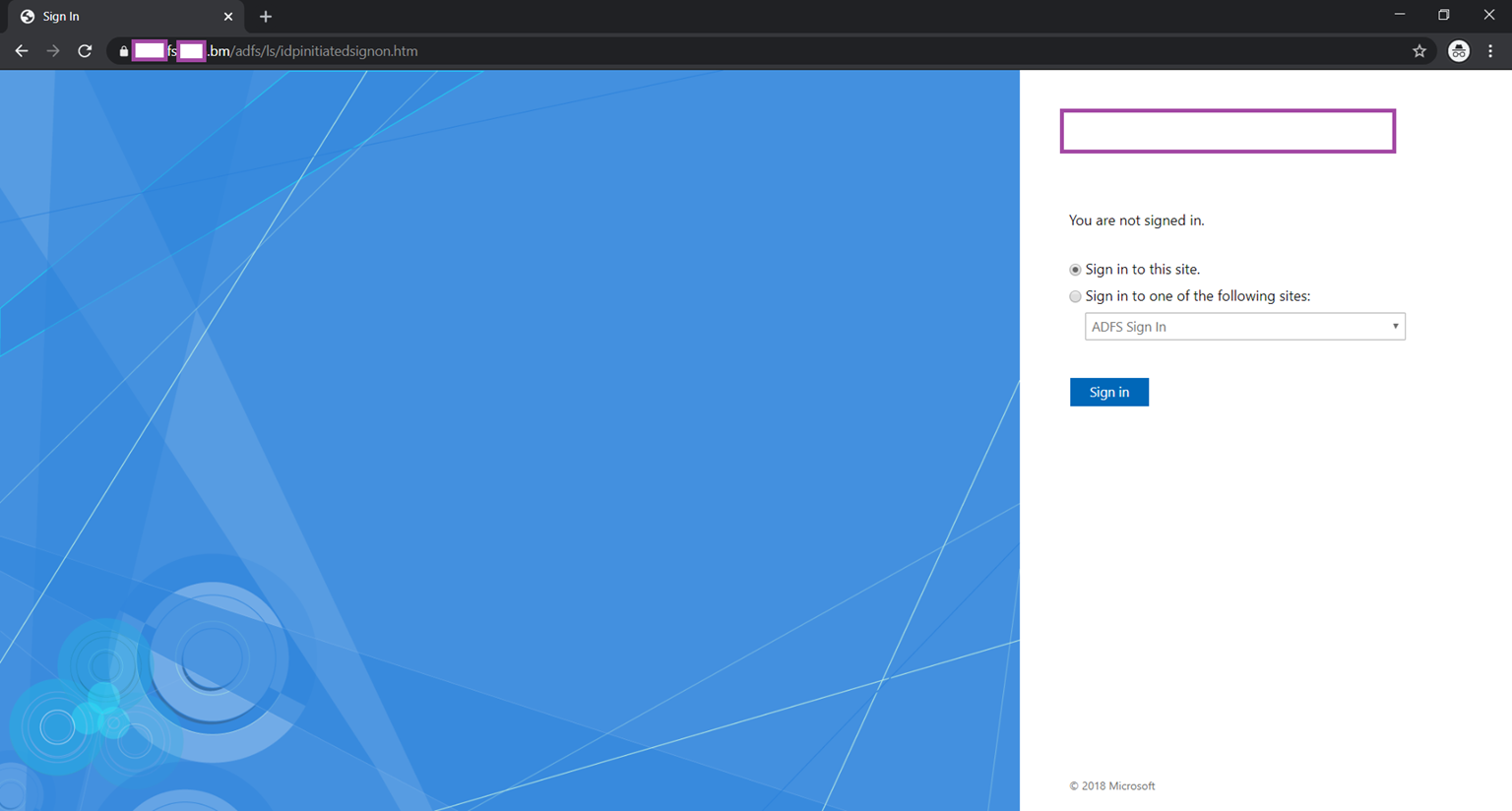
If you do not have any Relaying Party Trusts configured but want to test the newly deployed Duo, you can use the idpinitiatedsignon.htm page to test.
Begin by enabling the page by executing the following cmdlet as ADFS 2016 and newer disables the page by default:
Set-AdfsProperties -EnableIdPInitiatedSignonPage $true
Verify that the sign on page is displayed when browsing to the URL: https://<ADFSServer>/adfs/ls/idpinitiatedsignon.htm
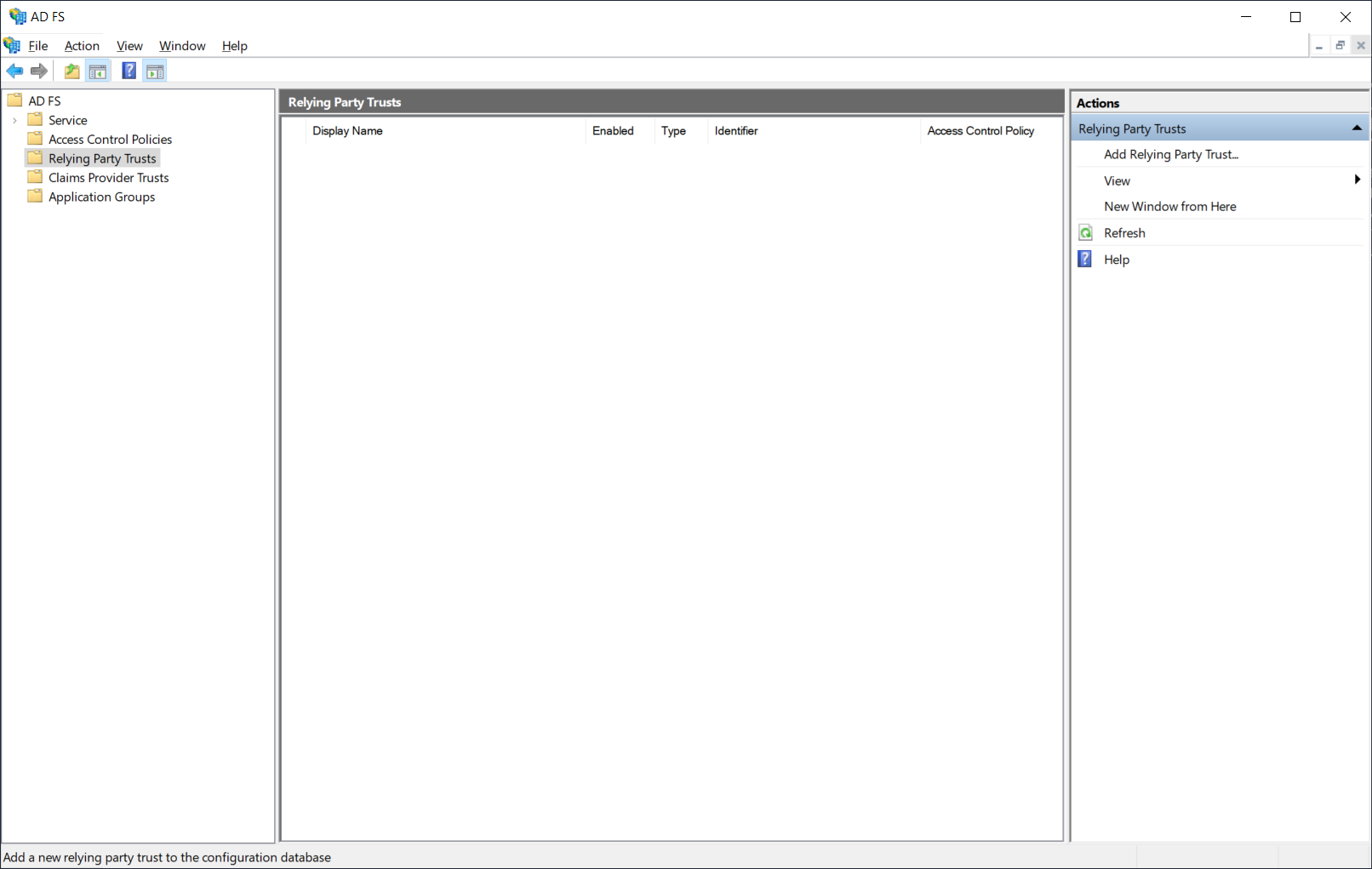
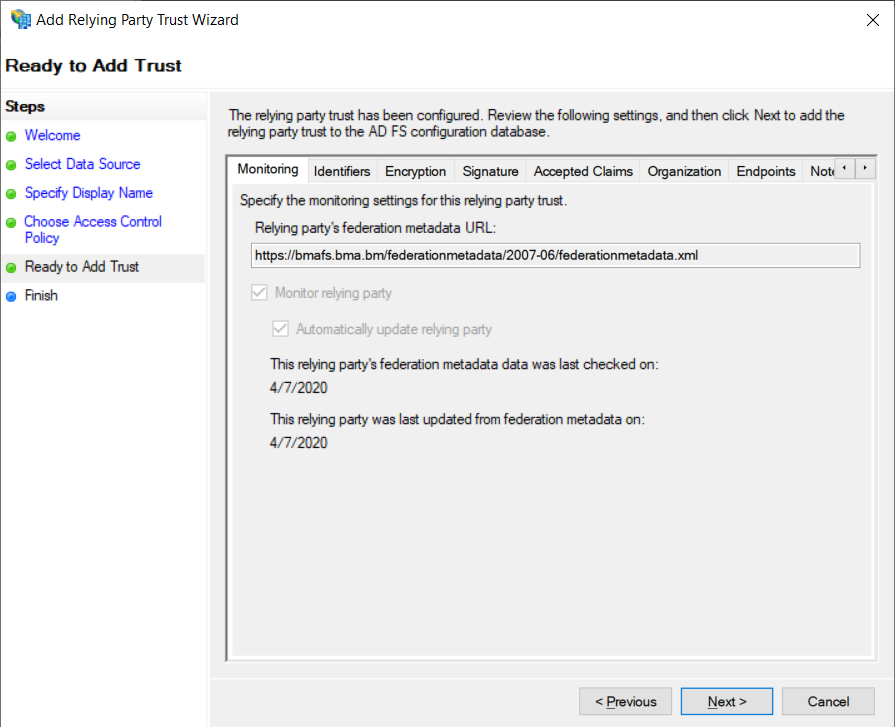
Navigate to AD FS > Relying Party Trusts and click on Add Relying Party Trust… under the Actions pane on the right:
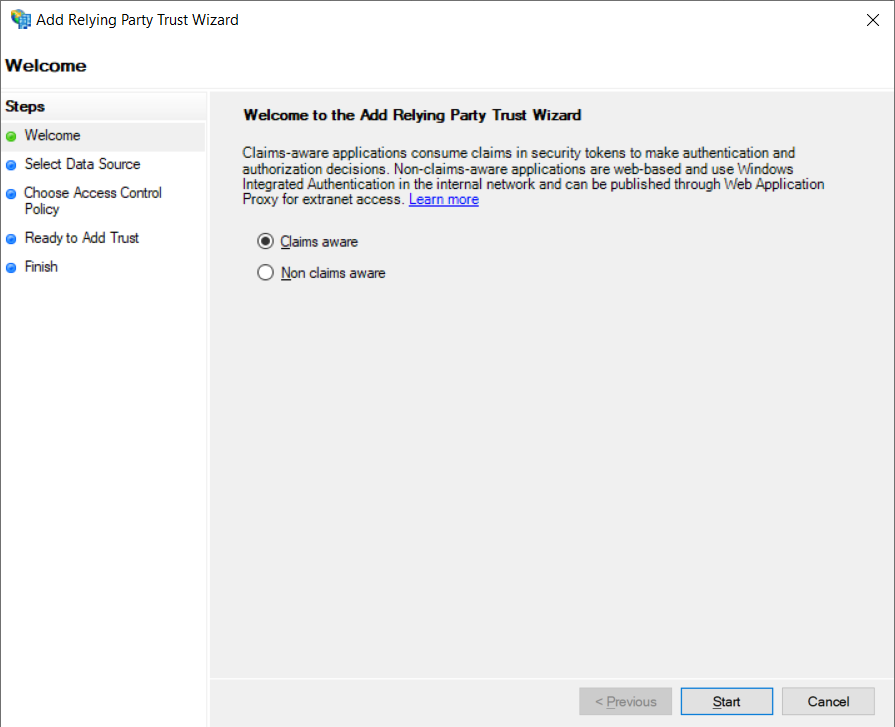
Select Claims Aware and click Start:
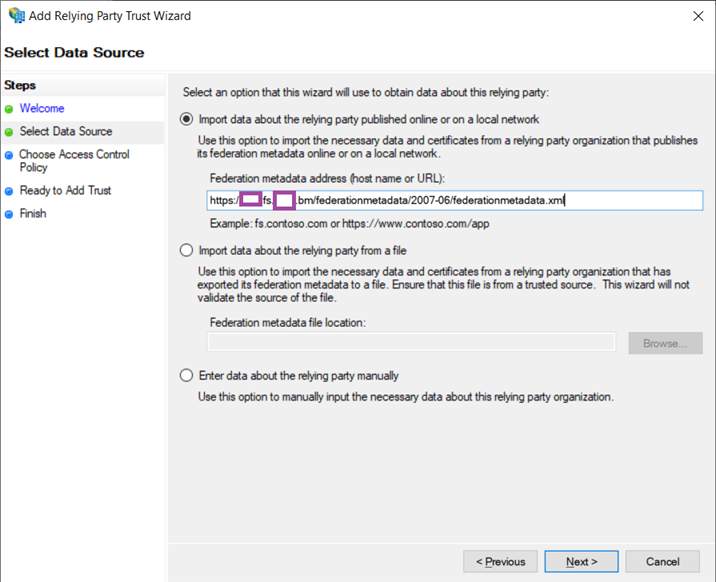
Select Import data about the relying party published online or on a local network and paste the following under the Federation metadata address (host name or URL): text field:
https://<ADFSServerFQDN>/federationmetadata/2007-06/federationmetadata.xml
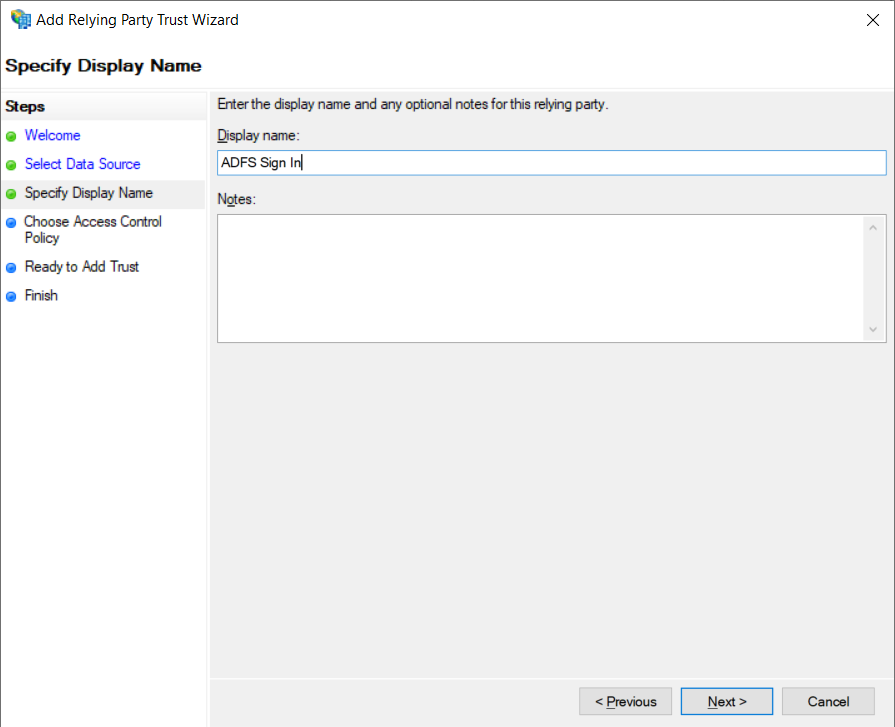
Specify a Display name and an optional description in the Notes field:
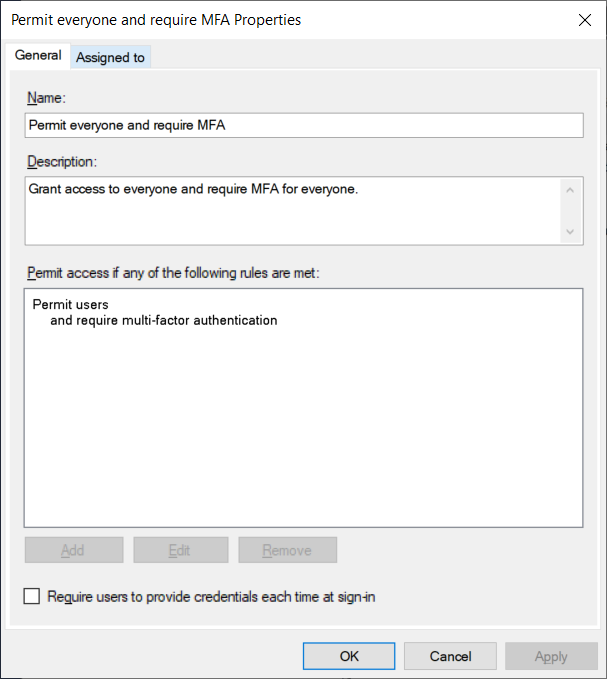
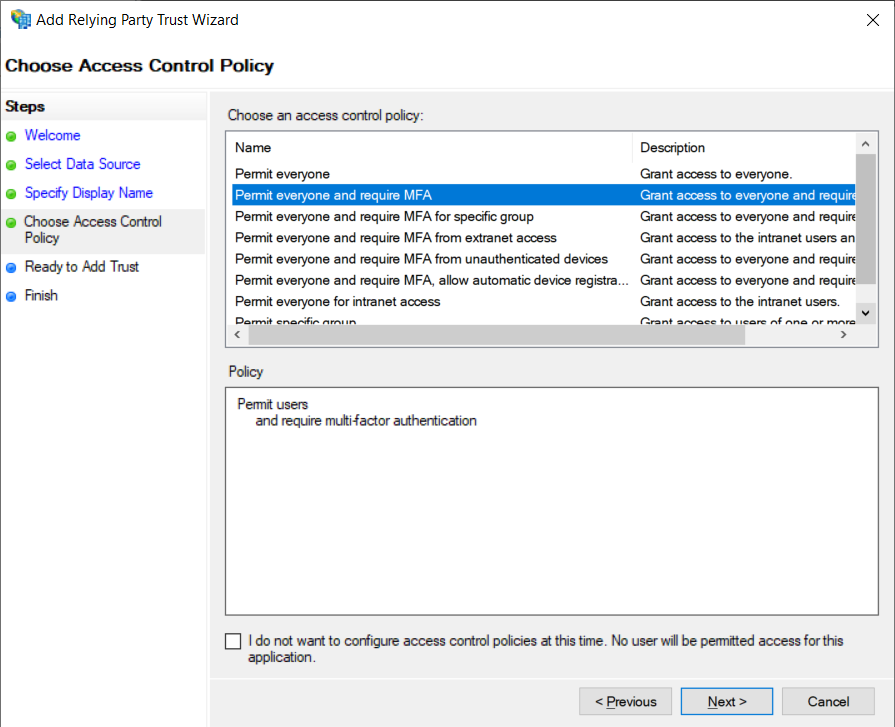
Select Permit everyone and require MFA under the Choose an access control policy options:
Verify the configuration and click Next:
Clear the Configure claims issuance policy for this application and click Close:
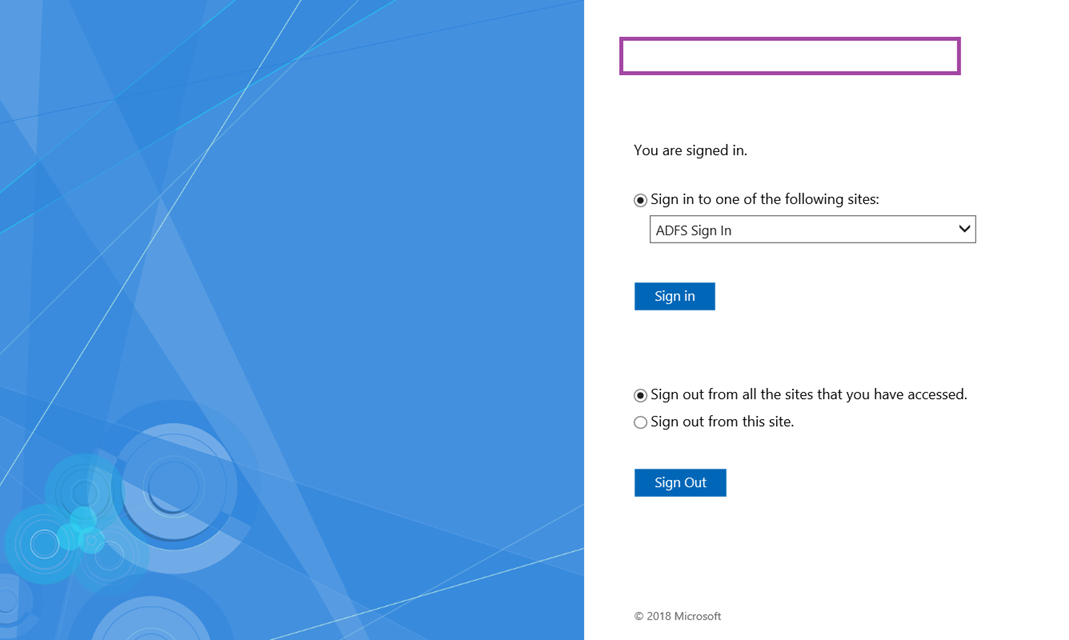
Navigate to the URL: https://<ADFSServer>/adfs/ls/idpinitiatedsignon.htm and you should see an additional Sign in to one of the following sites: option. Ignore that option and proceed to sign with the Sign in to this site option:
Enter your Active Directory credentials:
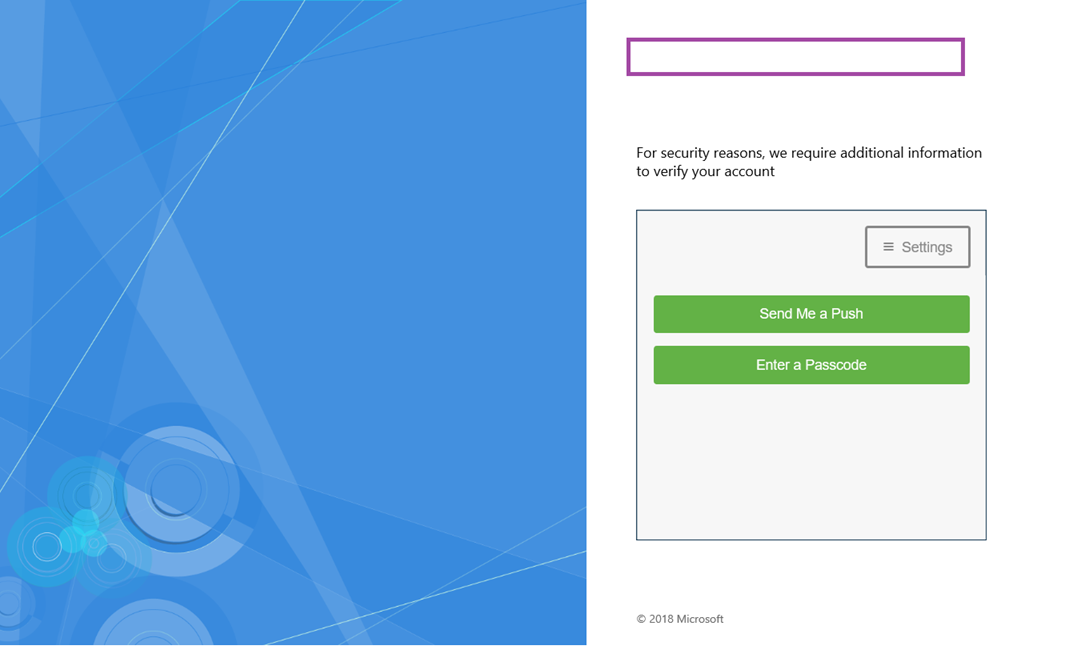
You should now see the Duo 2-factor authentication prompt:
The following page will be displayed upon successfully signed in: